- Products
- License Management ➤
- Discovery ➤
- SaaS Optimization ➤
- Oracle Optimization ➤
- Optimization for SAP® ➤
- Cloud Cost Management ➤
- Optimization for Engineering Software ➤
- Services
- SAM Services ➤
- Products
- Knowledge Management for Customer Service ➤
- Knowledge Management for IT ➤
- Knowledge Management for Enterprise Services ➤
- Chatbots ➤
- Services
- Professional Services ➤
- Industries
- Automotive ➤
- Finance and Insurance ➤
- Manufacturing ➤
- Products
- IT Service Desk ➤
- IT Self-Service ➤
- IT Service Catalog & SLA ➤
- IT Asset Management ➤
- IT Change & Configuration Management ➤
- IT Financial Management ➤
- IT Monitoring ➤
- IT Service Portfolio & Service Design ➤
- IT Project Portfolio Management ➤
- IT Governance, Risk & Compliance ➤
- Enterprise Service Management ➤
- Hybrid Cloud Management ➤
- Knowledge Management for IT ➤
- Products
- IT Event Management ➤
- System Monitoring ➤
- Cloud Monitoring ➤
- End-to-End Monitoring ➤
- Service Monitoring ➤
- IT Service Alerting ➤
- Services
- Professional Services & Training ➤
- Services
- Digital Experience ➤
- Digital Process Automation ➤
- Application Management Services ➤
- E-Government Solutions ➤
- Expert Staffing ➤
- Custom Software Development ➤
- Technology Partners
- Liferay DXP ➤
- Pega ➤
- Disy Informationssysteme ➤

USU IT Service Management (ITSM)
High Performance ITSM Tool
USU IT Service Management (ITSM) is your comprehensive software solution covering standard ITSM processes plus additional service areas in your company.
Use ITSM as your central tool for enterprise service management across your company and to automate processes across departments. Smoothly manage your complex service processes, on-premises or in the cloud, with a scalable solution that grows with your needs. With everything you need to plan, operate and control your IT, our range of mix-and-match modules and artificial intelligence (AI) applications enable you to get everything you need, and nothing you don’t.
We feature proven maximum ITIL® compliance. Therefore, the USU ITSM software suite is one of the top verified tools worldwide - as confirmed by Pink Elephant and SERVIEW.
Your Benefits
> 1 M € savings per year with 5,000 employees
40 % higher employee satisfaction
10 x faster service processes
USU IT Service Management
- IT Service Desk
- IT Self-Service Management
- IT Asset Management
- IT Change & Configuration Management
- IT Service Catalog & SLA
- IT Service Portfolio & Service Design
- IT Project Portfolio Management
- IT Financial Management
- Governance, Risk & Compliance
- IT Monitoring
- Knowledge Management for IT
- Hybrid Cloud Management
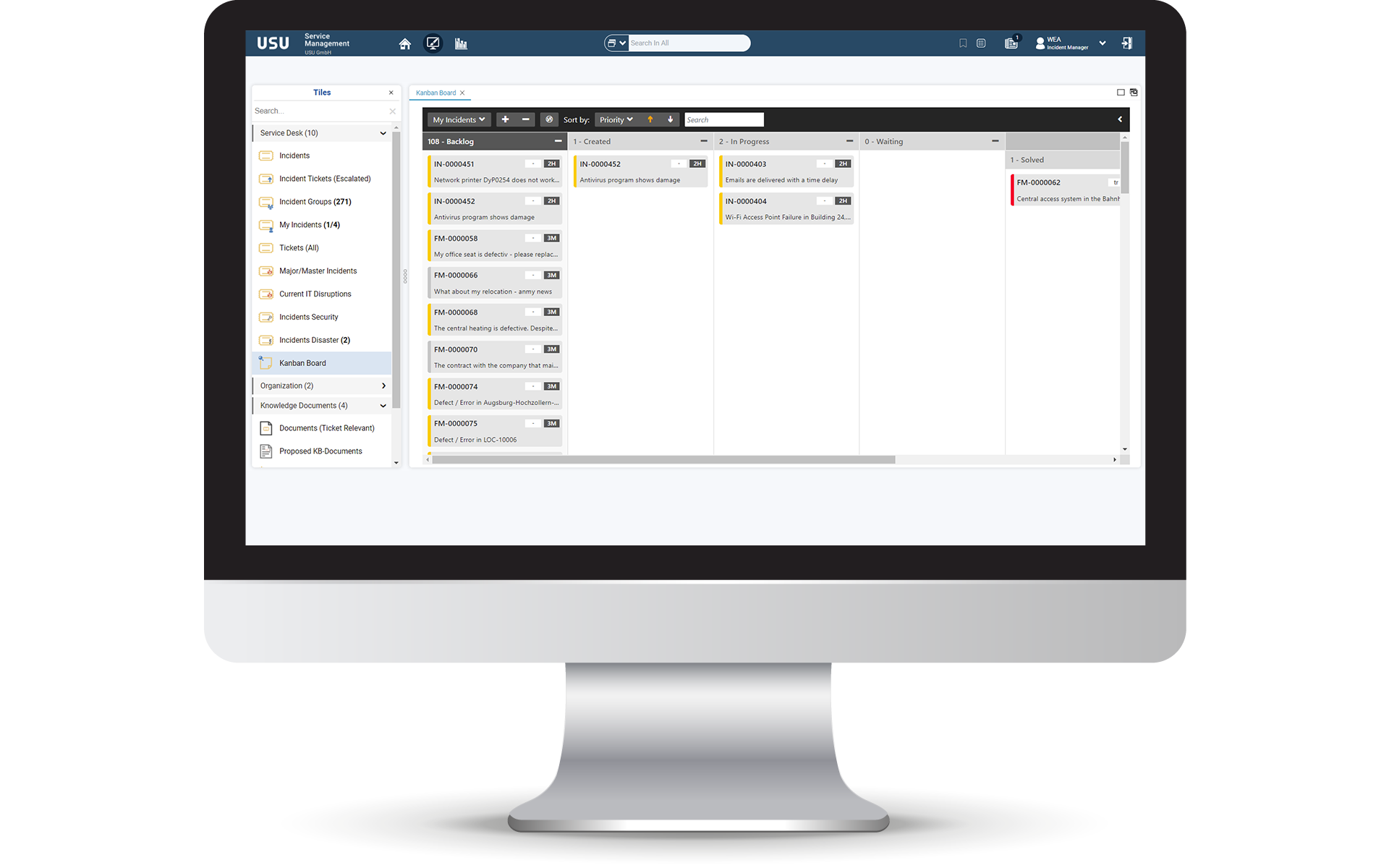
IT Service Desk
The modular all-in-one solution for your IT support
Create, analyze, and process IT tickets efficiently with our IT Service Desk. You benefit with up to 20% of end-user questions answered and reported incidents resolved and up to 100% of service requests processed — all automatically.
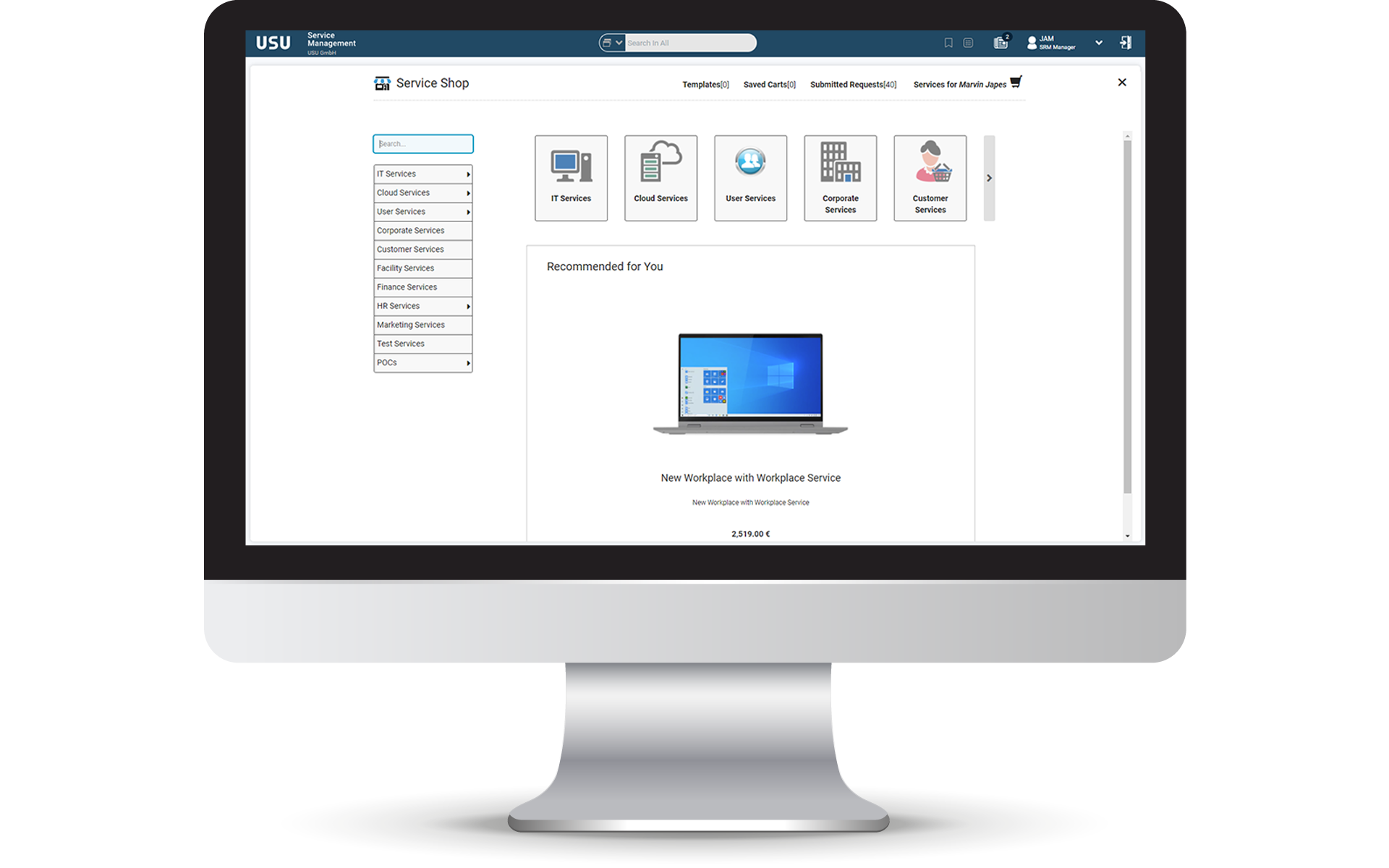
IT Self-Service Management
Using Self-healing opportunities
Deliver rapid, reliable and on-demand IT support. With a suite of IT Self-Service tools, you can reduce your IT tickets amount immensely and increase your user satisfaction. Deliver innovative solutions an quick answers to your users requests.
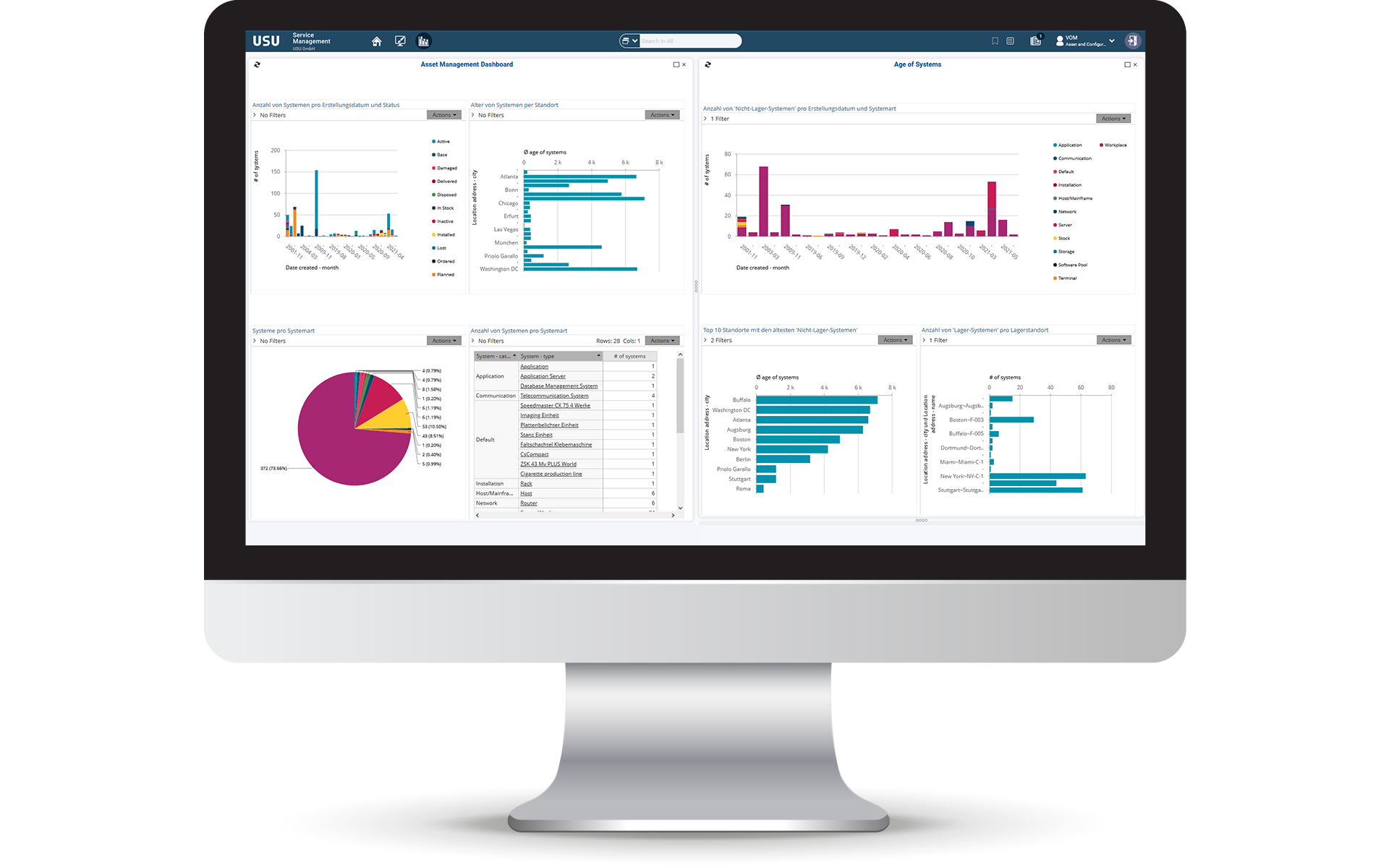
IT Asset Management
Deep dive into your IT assets
Manage your IT assets throughout their entire lifecycle. We support you in controlling your entire hardware and software, virtual or physical assets, on-premises or in the cloud. Always know what you use and own.
IT Change & Configuration Management
ITIL®-compliant CMDB
Get a comprehensive overview of your IT infrastructure and depend on our Configuration Management Database (CMDB). We support you to recognize dependencies and risks so you can ensure uninterrupted and secured IT operations.

IT Service Catalog & SLA
Increase governance and operational efficiency
Use a personalizable service catalog, which transparently displays all IT and business services that can be ordered. All of your customers' service instances, including applicable service level agreements (SLAs), become transparent.
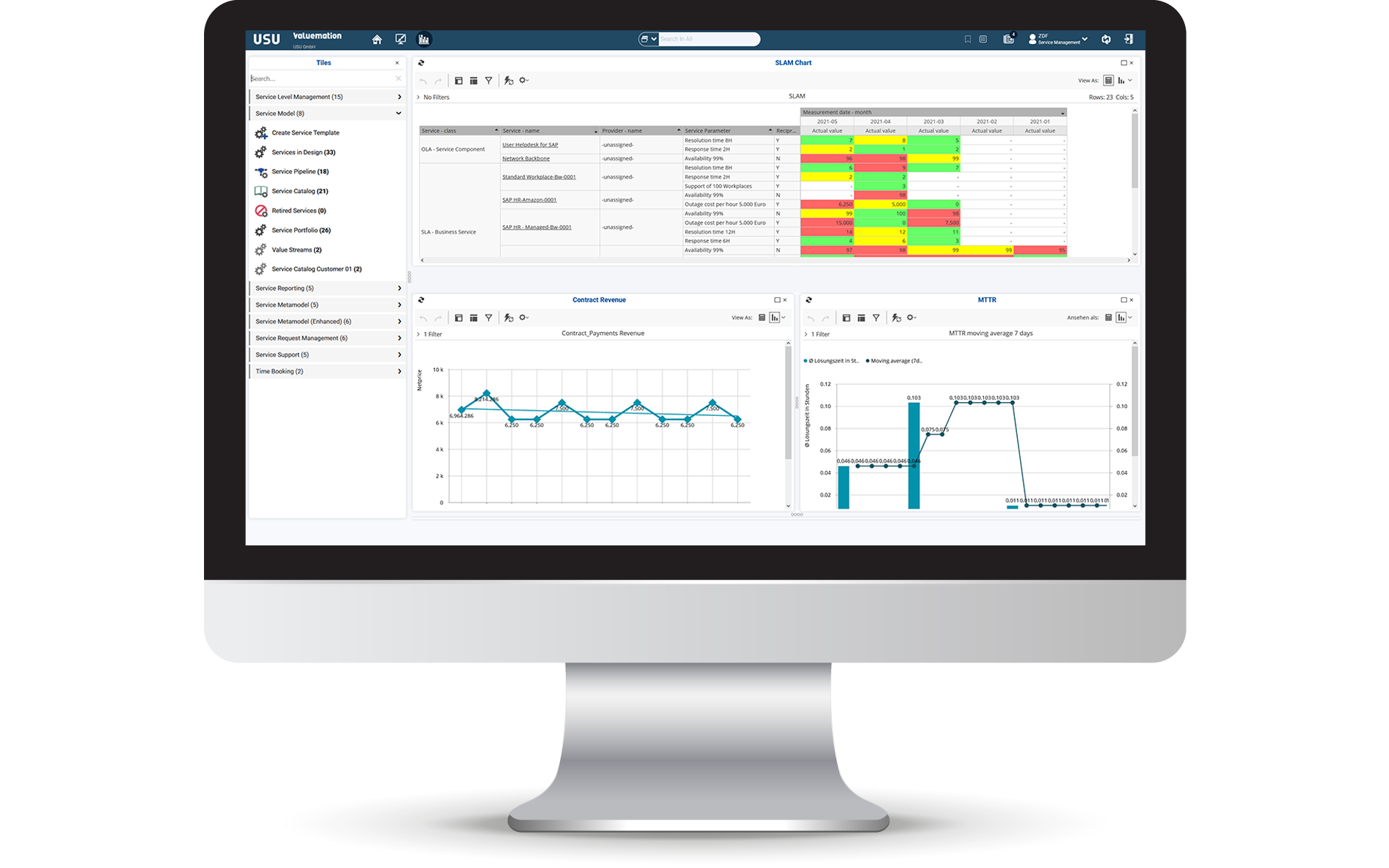
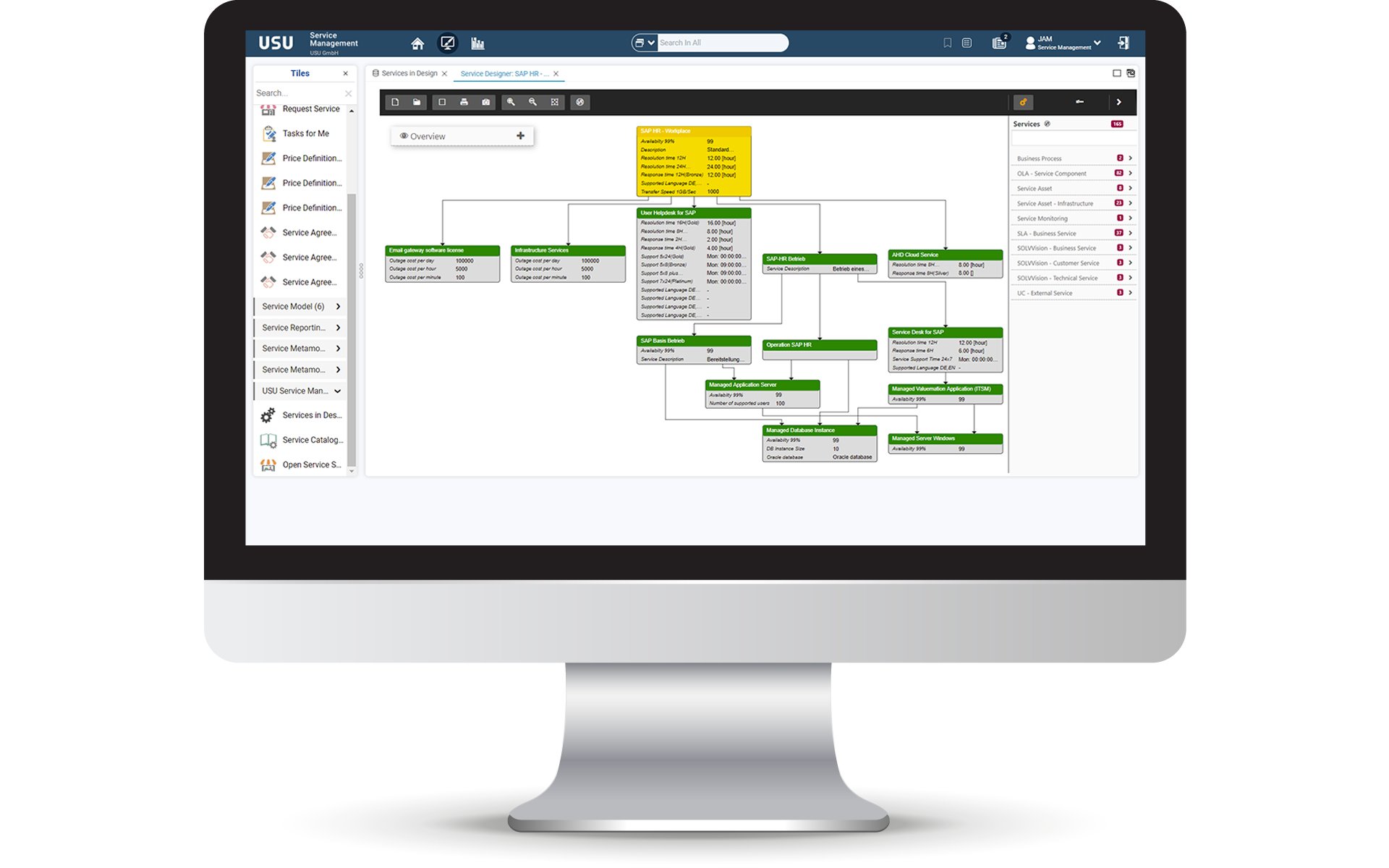
IT Service Portfolio & Service Design
Manage your business and IT services
Increase value creation and start managing your business and IT services — from planning and specification to operation and decommissioning. Get an overview of the service spectrum of your IT service organization.
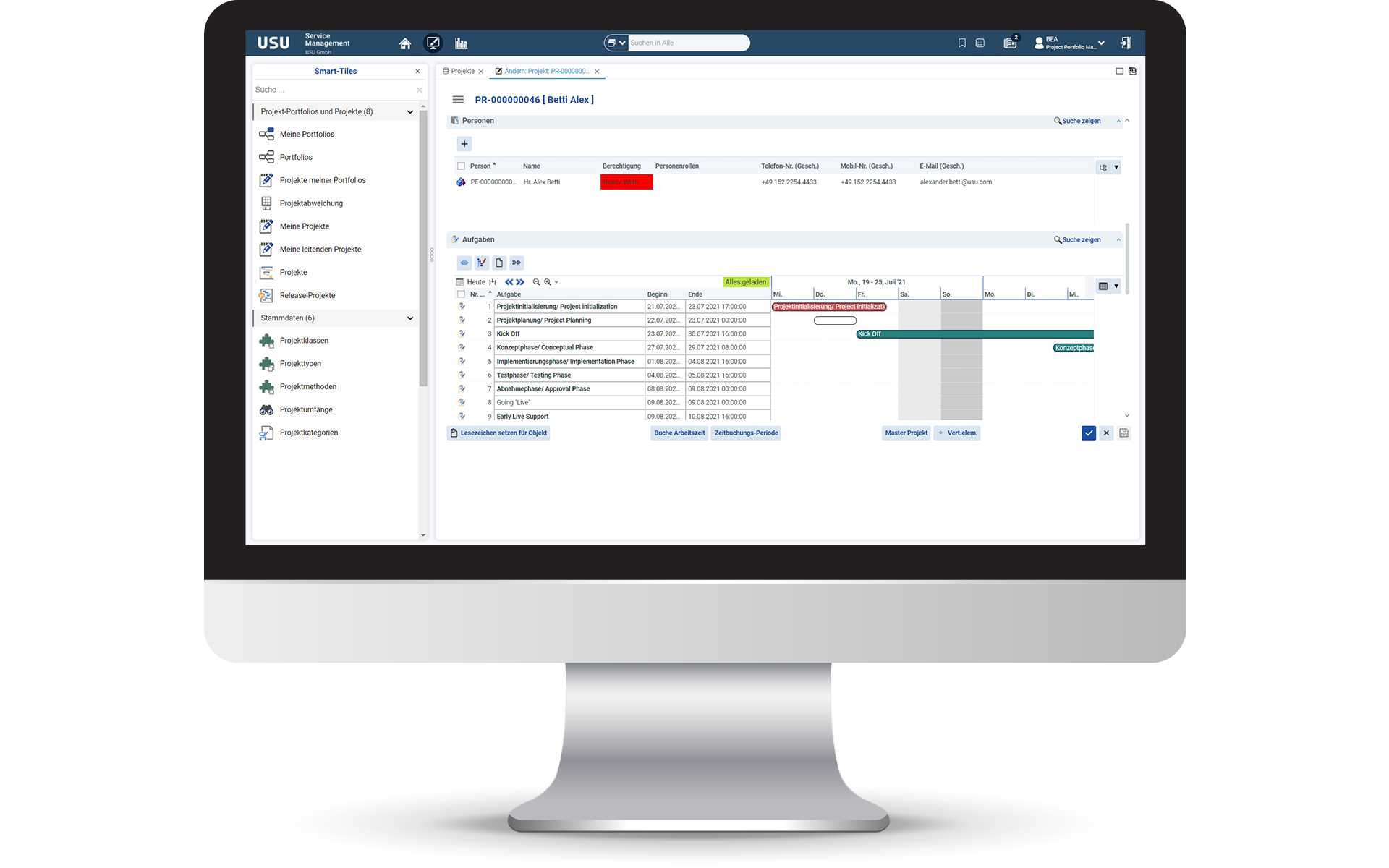
IT Project Portfolio Management
Gain control of your IT landscape
Efficient control of your IT projects. Plan, manage and control all programs, resources and project portfolios with just one software solution. Get more visibility in all your work and keep control over all activities.
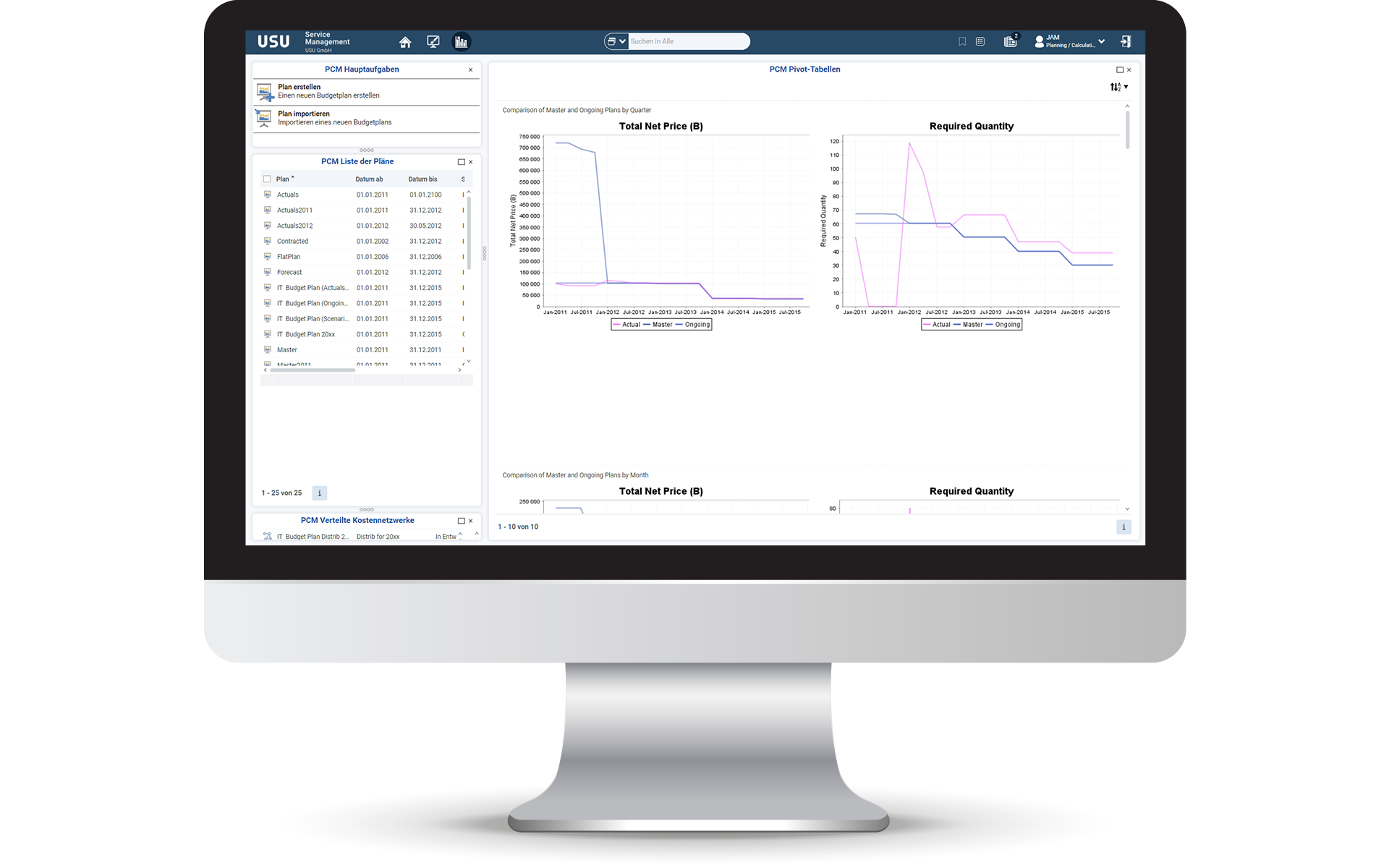
IT Financial Management
Determine service unit costs the easy way
Efficiently and transparently manage your IT service costs with our IT Financial Management solution. Save time planning your IT budget and show your service units exactly which items comprise the service costs.
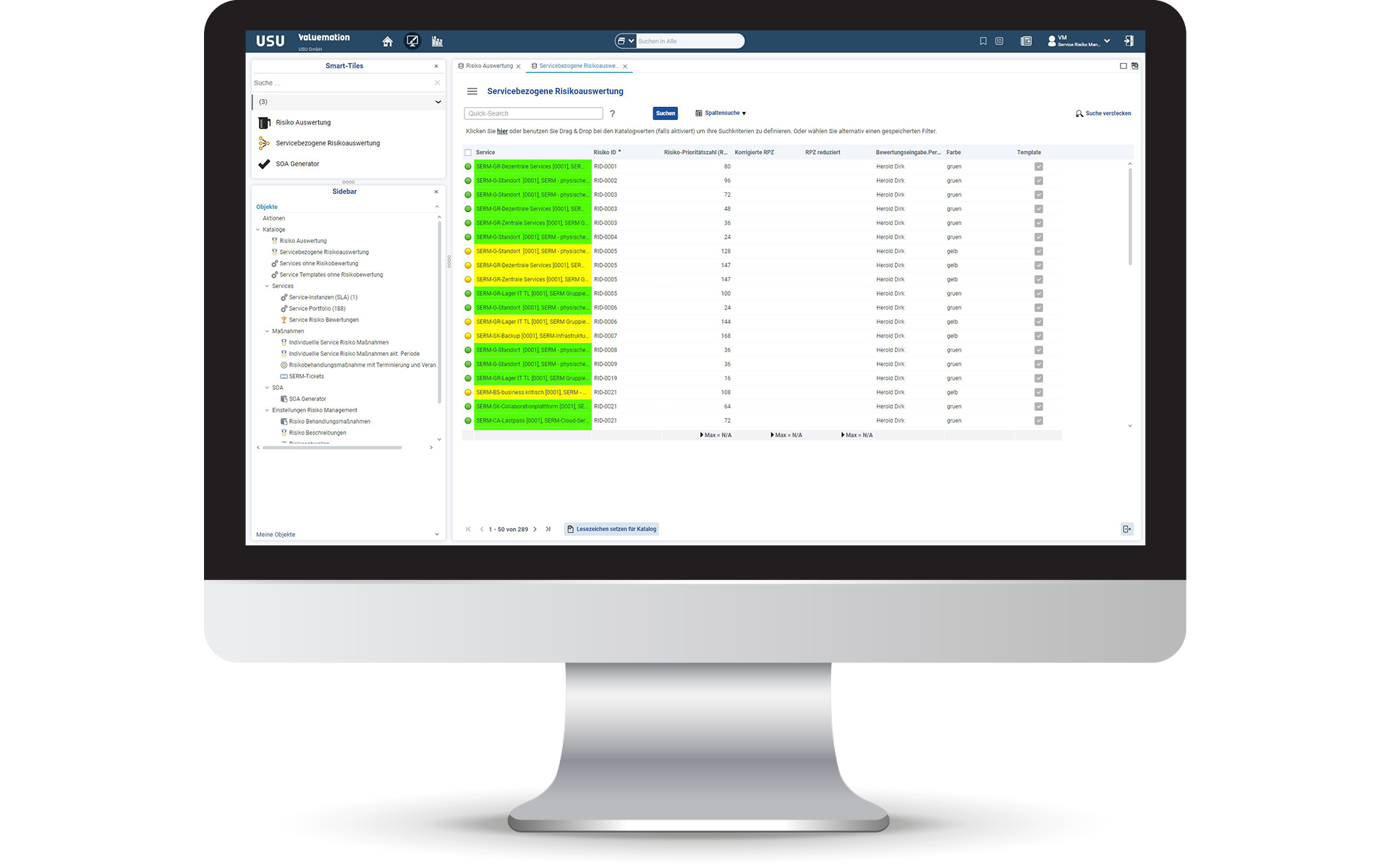
Governance, Risk & Compliance
Reduce risks in IT operations
Track and manage all your risks in IT operations with a risk catalog for ISO 27001 assessment including the 27017/27018 extension. Risk priority values identify the most important risks. Applying preventing measures causes the risk priority value to be decreased.
A risk catalog for ISO 27001 assessment including the 27017/27018 extension is included out-of-the-box.
IT Monitoring
Get a complete overview of your entire infrastructure
Continuously monitor and manage your hybrid IT architecture with just one solution. Get a comprehensive, centralized view of your IT landscape and services. No matter where they run: on-premises or in the Cloud.

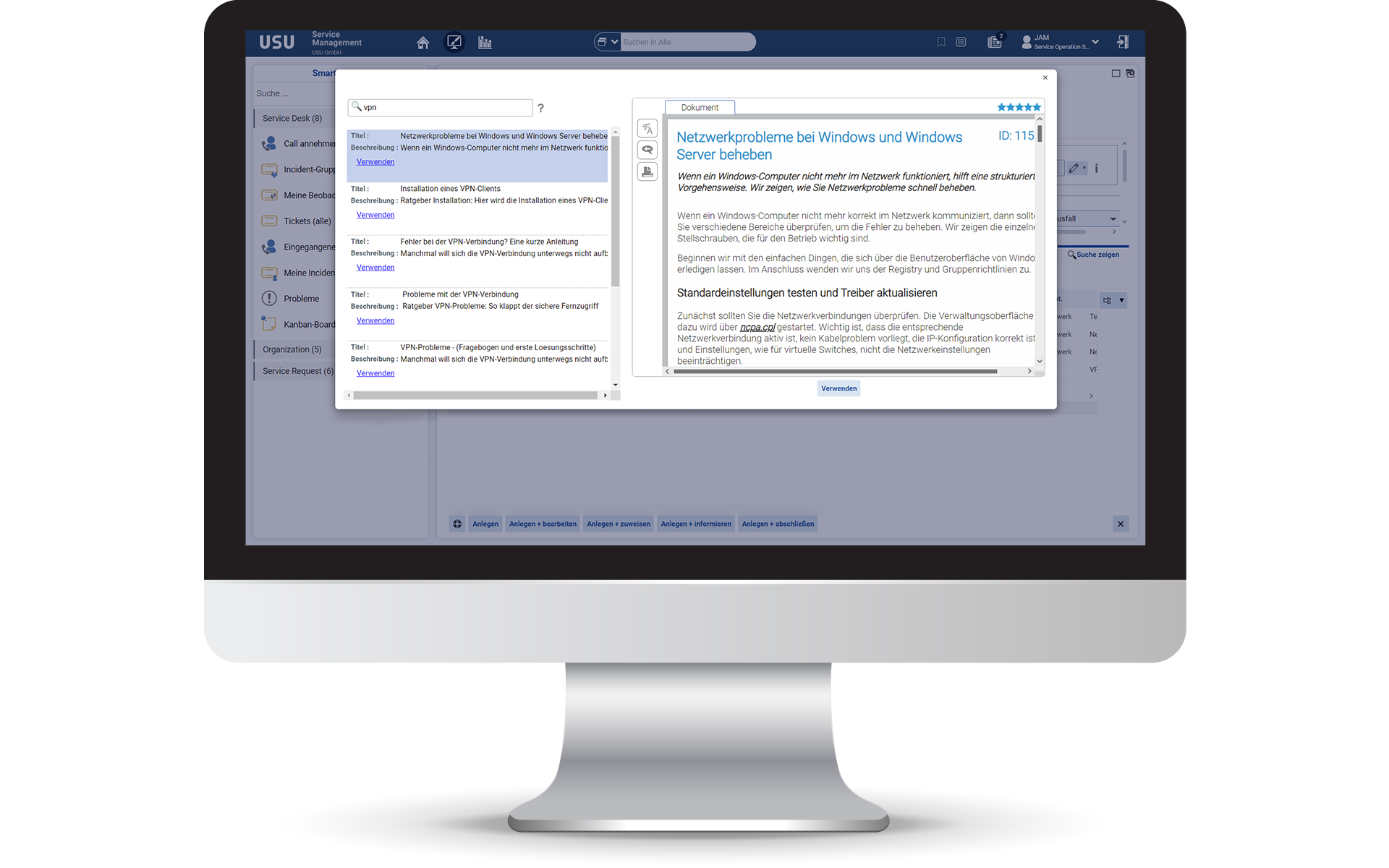
Knowledge Management for IT
Predictive Knowledge Management
Start with successful knowledge management in IT support and create an enhanced service experience. Comply with service level agreements, improve service quality, and deliver quick, conclusive answers to your service customer inquiries.
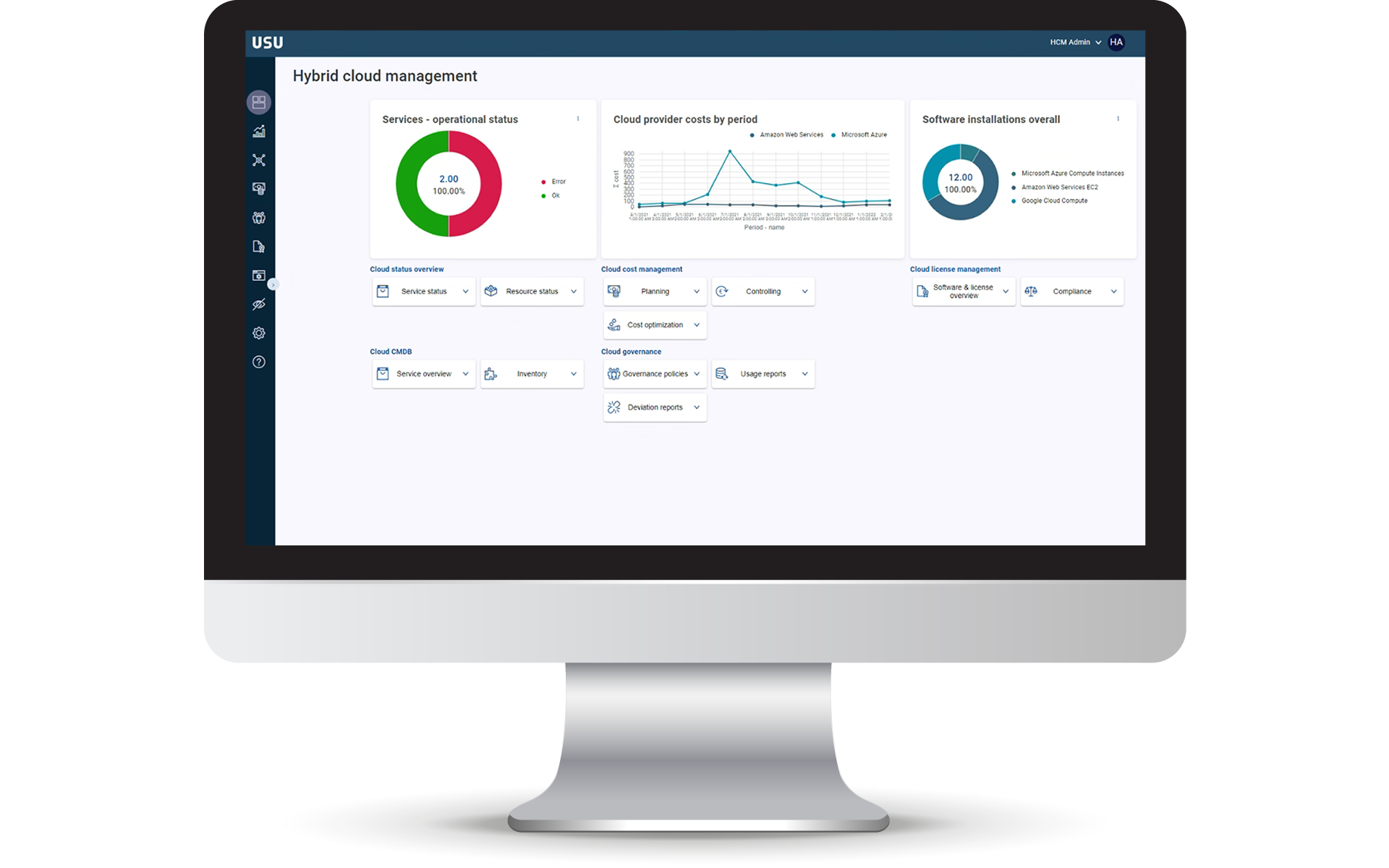
Hybrid Cloud Management
Manage your entire cloud infrastructure
The all-in-one modular solution for consolidated administration of your cloud infrastructure — hybrid or multi cloud. Manage all your cloud resources (IaaS, PaaS & SaaS) and start to optimize your cloud costs sustainably.
USU IT Service Management
IT Service Desk
The modular all-in-one solution for your IT support
Create, analyze, and process IT tickets efficiently with our IT Service Desk. You benefit with up to 20% of end-user questions answered and reported incidents resolved and up to 100% of service requests processed — all automatically.
IT Self-Service Management
Using Self-healing opportunities
Deliver rapid, reliable and on-demand IT support. With a suite of IT Self-Service tools, you can reduce your IT tickets amount immensely and increase your user satisfaction. Deliver innovative solutions an quick answers to your users requests.
IT Asset Management
Deep dive into your IT assets
Manage your IT assets throughout their entire lifecycle. We support you in controlling your entire hardware and software, virtual or physical assets, on-premises or in the cloud. Always know what you use and own.
IT Change & Configuration Management
ITIL®-compliant CMDB
Get a comprehensive overview of your IT infrastructure and depend on our Configuration Management Database (CMDB). We support you to recognize dependencies and risks so you can ensure uninterrupted and secured IT operations.
IT Service Catalog & SLA
Increase governance and operational efficiency
Use a personalizable service catalog, which transparently displays all IT and business services that can be ordered. All of your customers' service instances, including applicable service level agreements (SLAs), become transparent.
IT Service Portfolio & Service Design
Manage your business and IT services
Increase value creation and start managing your business and IT services — from planning and specification to operation and decommissioning. Get an overview of the service spectrum of your IT service organization.
IT Project Portfolio Management
Gain control of your IT landscape
Efficient control of your IT projects. Plan, manage and control all programs, resources and project portfolios with just one software solution. Get more visibility in all your work and keep control over all activities.
IT Financial Management
Determine service unit costs the easy way
Efficiently and transparently manage your IT service costs with our IT Financial Management solution. Save time planning your IT budget and show your service units exactly which items comprise the service costs.
Governance, Risk & Compliance
Reduce risks in IT operations
Track and manage all your risks in IT operations with a risk catalog for ISO 27001 assessment including the 27017/27018 extension. Risk priority values identify the most important risks. Applying preventing measures causes the risk priority value to be decreased.
A risk catalog for ISO 27001 assessment including the 27017/27018 extension is included out-of-the-box.
IT Monitoring
Get a complete overview of your entire infrastructure
Continuously monitor and manage your hybrid IT architecture with just one solution. Get a comprehensive, centralized view of your IT landscape and services. No matter where they run: on-premises or in the Cloud.
Knowledge Management for IT
Predictive Knowledge Management
Start with successful knowledge management in IT support and create an enhanced service experience. Comply with service level agreements, improve service quality, and deliver quick, conclusive answers to your service customer inquiries.
Hybrid Cloud Management
Manage your entire cloud infrastructure
The all-in-one modular solution for consolidated administration of your cloud infrastructure — hybrid or multi cloud. Manage all your cloud resources (IaaS, PaaS & SaaS) and start to optimize your cloud costs sustainably.
Happy Customers

Service requirements on the rise
The German Federal Employment Agency (BA) operates one of the largest IT system landscapes in Germany, with 160,000 networked PC workstations, 9,000 servers and a processing volume of, for instance, 39 million emails and 16 million bank transfers every month.
About the project
Success thanks to a customer-focused business model
Jungheinrich AG provides support for its customers and their investment goods over the entire lifecycle and focuses on customer benefits. IT plays a key role when implementing this strategy.
About the project
The challenge
As part of the strategic realignment of Bosch IT into a service organization, the entire portfolio as well as the planning, calculation and billing of IT services is to be redefined, structured and implemented.
About the project
Smart Businesses use USU IT Service Management
We’ve been a reliable and innovative partner in IT and enterprise service management for more than 40 years. That’s proven by our excellent references.
Features
We deliver standard features so you can get going right away. But we can do so much more as well: We help you to customize the software to meet your needs. There’s practically no limits to what you can do. We provide the features you need to adapt and integrate our software.
Flexible Workflows
Customize the standard workflows included in the scope of delivery and add any other workflows.
Automate Processes
Automate processes so they run independently without having to manually intervene, even across multiple systems.
System Integration
Use out-of-the-box connectors or a rich set of programming interfaces to integrate with any 3rd party systems.
Open Data Model
Introduce custom attributes and data objects to run processes on custom data such as non-IT assets.
Roles and Permissions
Configure roles and permissions to implement your access privileges of users, groups or multiple tenants.
Develop, Test and Run
Use built-in developer features to develop, test and run, securely moving changes between multiple stages.
Certified and Recognized